In the evolution of cloud-native security, identity has become the new perimeter. As enterprises migrate to distributed, multi-cloud architectures, the traditional security model of static credentials and network-based trust is giving way to a Zero Trust paradigm where every workload, service, and user must continuously prove their identity through cryptographic verification.
We are giving you a first look at an upcoming foundational enhancement to the CockroachDB authentication stack: native support for Subject Alternative Name (SAN) fields in X.509 certificates.
This change is designed to eliminate legacy authentication constraints and, more importantly, unlock seamless integration with the industry standards for automated workload identity, SPIFFE (Secure Production Identity Framework for Everyone) and SPIRE (the SPIFFE Runtime Environment).
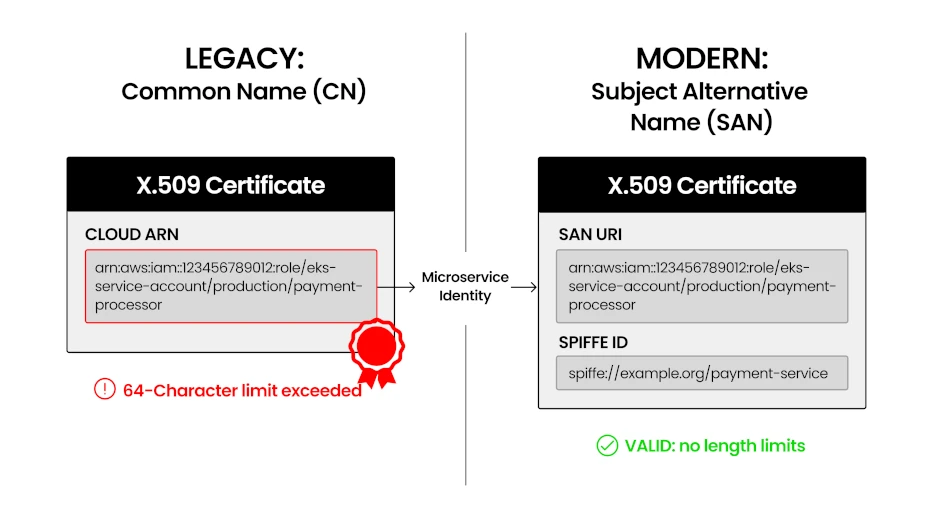
Historically, many databases including earlier versions of CockroachDB relied exclusively on the Common Name (CN) field in certificates for user authentication. While this served the industry for decades, it creates significant friction in modern environments:
The 64-Character Limit: The CN field is restricted to 64 characters per RFC 5280. Modern cloud-native identities, such as an AWS IAM role (e.g.,
arn:aws:iam::123456789012:role/eks-service-account/production/payment-processor), can easily reach 73+ characters.Eliminating Compromises: Previously, long identities forced teams to use "hashing" or "truncation" workarounds, which sacrifice the auditability and clarity that makes certificates attractive.
Modern Compliance: RFC 9110 explicitly deprecates the CN field for identity verification. Our upcoming SAN support allows you to use URI, DNS, and IP values, helping organizations meet SOC 2 requirements.
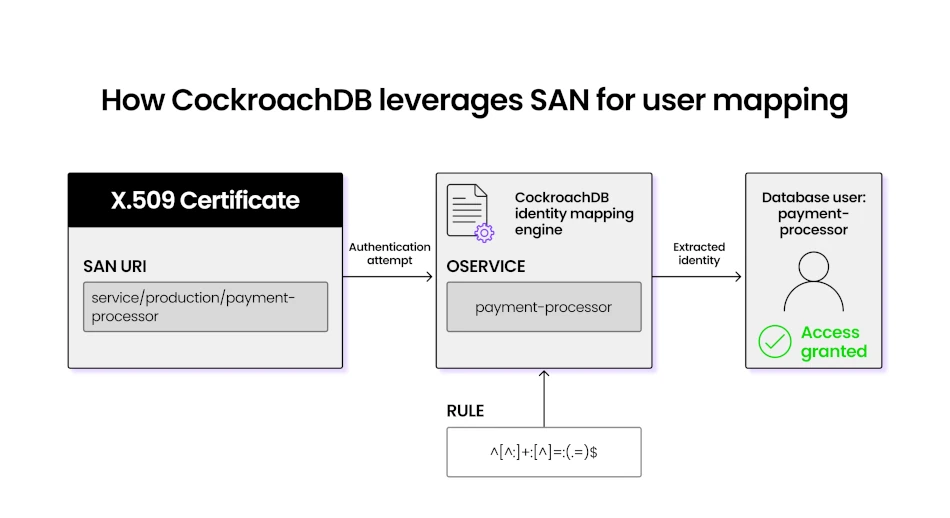
How CockroachDB Leverages SAN for User Mapping
Beyond simply reading the SAN field, CockroachDB is introducing a powerful Identity Mapping engine that translates complex certificate metadata into database users. This upcoming feature allows administrators to define flexible, pattern-based rules using regular expressions (Regex).
Instead of manually creating a database user for every individual microservice, you can define a single global rule. For example, if your certificates contain a URI such as service:production:payment-processor, CockroachDB can be configured to:
Pattern Match: Use regex to parse the URI and identify the specific workload identity (e.g., matching the string after the final colon).
Validate Identity: Ensure the identity presented in the certificate matches the SQL username the client is claiming to be.
Dynamic Mapping: Automatically grant access based on that cryptographic proof, allowing your security policy to scale as you deploy new services without requiring manual database updates for every new certificate.
Unlocking Zero Trust: The Power of SPIFFE and SPIRE
The technical bridge provided by SAN support is what enables CockroachDB to integrate with SPIFFE and SPIRE.
At its core, SPIFFE defines a standard way for software services to identify themselves across heterogeneous environments. It provides a uniform identity format called a SPIFFE ID, structured as a URI (e.g., spiffe://trust-domain/workload-name). SPIRE is the implementation that brings this to life; it performs workload-attestation, verifying the software's characteristics against its environment (like a Kubernetes Namespace or an AWS Instance ID) and then automatically issues a short-lived, cryptographically signed certificate containing that SPIFFE ID.
Why This Matters for Your Infrastructure:
By moving the source of truth from a static password to a dynamic SPIFFE ID, organizations achieve:
Zero Static Secrets: No passwords, API keys, or long-lived certificates are stored in environment variables, Kubernetes secrets, or third-party secret managers. This removes the "secret sprawl" that leads to most modern breaches.
Least Privilege Enforcement: Because identities are issued based on real-time attestation, each workload receives only the specific identity and database permissions it needs for its current context.
Multi-Cloud Portability: SPIFFE provides a vendor-neutral abstraction. Unlike cloud-specific identity tools (like IAM roles), a SPIFFE ID provides a consistent identity layer across AWS, Azure, GCP, and on-premises environments, ensuring your authentication remains portable and prevents vendor lock-in.
No Human Intervention: Credentials rotate automatically (often every hour or even minutes), drastically shrinking the window of vulnerability. No human ever touches, rotates, or manually stores a database secret again.
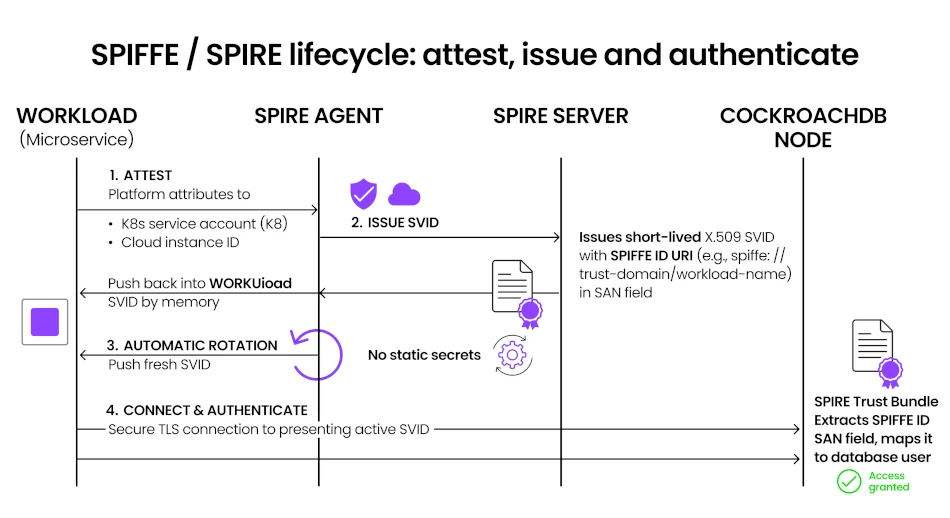
How SPIFFE/SPIRE Works with CockroachDB
When this feature arrives in 26.2, CockroachDB will participate as a first-class citizen in your Zero Trust architecture. The lifecycle of a secure connection follows a fully automated "Attest, Issue, and Authenticate" loop:
Workload Attestation: When a service (the "Workload") starts up, it contacts a local SPIRE Agent. The Agent inspects the workload's attributes—such as its Linux UID, Kubernetes Service Account, or Cloud Instance ID—to verify its identity.
SVID Issuance: Once verified, the SPIRE Server issues a SPIFFE Verifiable Identity Document (SVID). This is a short-lived X.509 certificate where the unique SPIFFE ID (e.g., spiffe://trust-domain/service) is encoded in the SAN URI field.
Automatic Rotation: The SPIRE Agent pushes this certificate directly into the workload's memory. As the certificate nears expiration (e.g., every hour), SPIRE automatically rotates it, ensuring the workload always has a valid, fresh identity without ever writing a secret to disk.
Authenticate: When the service connects to CockroachDB, it presents this SVID. CockroachDB:
Validates the certificate against the configured SPIRE Trust Bundle.
Extracts the identity from the SAN field.
Maps that identity to a database user via the new Identity Mapping engine.
Access Granted: The workload is granted access to its specific tables and data—all without passwords, manual certificate management, or human intervention.
Ready to modernize your database authentication for a Zero Trust world? Speak with a Cockroach Labs expert.
Try CockroachDB Today
Spin up your first CockroachDB Cloud cluster in minutes. Start with $400 in free credits. Or get a free 30-day trial of CockroachDB Enterprise on self-hosted environments.
Sanchit Khanna is a Member of Technical Staff in Product Security at Cockroach Labs. His work spans the security spectrum, from engineering high-assurance backup storage systems to leading product-level security initiatives. He focuses on modernizing how organizations handle identity and access, to build architectures that are as resilient as they are secure.
Biplav Saraf is a Staff Product Manager at Cockroach Labs. He works across product security and developer experience, delivering built-in trust to unlock enterprise adoption in regulated industries, while creating an intuitive developer platform that lowers barriers to innovation.